Everyone loves the functionality of Splunk and nobody likes the price tag
SentinelOne Can Make Your Splunk:
Better – Faster – Cheaper
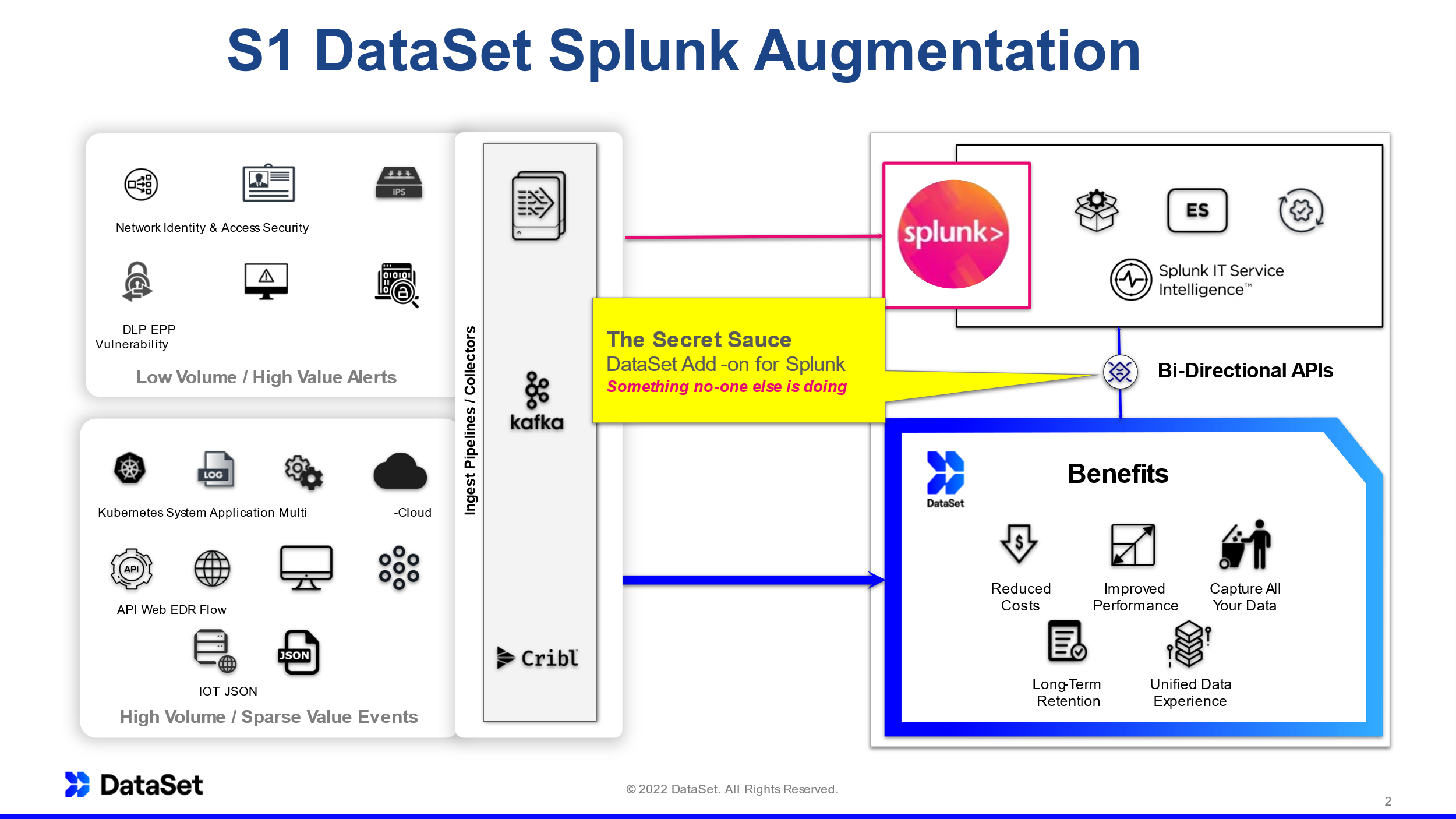
Splunk is a very mature, feature rich and powerful product, but it is extremely expensive to the point where many organizations can no longer afford to ingest all the data they want and some are even looking for alternatives. SentinelOne can give them the best of both worlds. We allow you to offload the data ingest to our enterprise logging platform but still query the data from Splunk. The result is this:
Keep using Splunk exactly the way you have been, but cut your bill in half or better and your queries will actually get faster.
Organizations need centralized visibility to security events so they can identify and automate response to threats and vulnerabilities. Often, security data is only visible in point solutions in their unique format, forcing companies to duplicate and move data to traditional SIEM solutions. These solutions were developed in the pre-cloud era, and when used as a data lake, they quickly become cost prohibitive and perform poorly.
Splunk Challenges
High Licensing Cost
Splunk has a single-tenant, monolithic architecture built for a pre-cloud, on-premises world. Splunk is not designed to auto-scale resulting in either over-provisioned or underperforming environments . By not leveraging the innovations available in the cloud, Splunk passes the inefficiency burden on to customers resulting in a very high cost of ownership.
Workarounds Are Expensive And Complex
Adding fuel to the fire, budgets have not kept pace with growing data volume. To contain their Splunk bill, companies have built workarounds including sampling, creating roll-ups, increasing cluster size, or using tiered storage. However, these workarounds create new complexities such as operational overhead and data loss, which in turn result in even higher costs and blind spots due to the missing data.
The Solution
01 | Augment Splunk with SentinelOne Security DataLake
SentinelOne Security DataLake centralizes event data across all sources and use cases from hybrid, multi-cloud, or on-premises environments. Customers use SentinelOne Security DataLake as a critical foundation of the security stack and to augment their SIEM by sending only high-volume data for high-value alerts to Splunk Enterprise Security, while retaining all data in the SentinelOne Security DataLake where it available to search directly inside of Splunk.
02 | Keep Your Splunk Workflows
We have built seamless integrations with Splunk so our customers get more from their existing investments without changing their Splunk experience. Query data stored in Security DataLake natively from Splunk. Build your Splunk dashboards, alerts, reports, and workflows just as you always have in Splunk – it just works!
03 | Hundreds of Supported Event Data Sources
Simple, easy-to-use ingestion mechanisms with all major data sources save 100s of hours needed to manually set up and configure data ingestion.
04 | Data Normalization for Faster Investigations
Memorizing field names and matching schema across multiple vendors are a thing of the past. SentinelOne Security DataLake can also normalize the incoming data to Open Cybersecurity Schema Framework (OCSF), an open standard so customers can quickly get value from their data.

05 | Positive ROI In Weeks
Delivering on our commitment to customer success, we include a white-glove joint success plan so customers achieve positive ROI within weeks without any heavy lifting from their teams.

Fill out the Form and Book a call with TOSS and an enterprise SentinelOne DataLake expert today for a free S1 DataSet Splunk Augmentation consultation.